
What Do We Mean By Hacking?
When we talk about “hacking” in terms of your digital portfolio, we are usually referencing “computer hacking.”
Hacking is the practice of modifying the features of a system, in order to accomplish a goal outside of the creator’s original purpose. The person who is consistently engaging in hacking activities, and has accepted hacking as a lifestyle and philosophy of their choice, is called a hacker.
Computer hacking pervades global society in the digital age. The act of breaking into a secure computer network serves many purposes, from corporate espionage to blatant theft and political insubordination. Computer hacking affects organizations in a variety of ways — some universal, others specific to the nature of the reason for hacking and the business in question. The direction of hacking — whether the organization hacks or gets hacked — also has an effect.
Hacking Is On The Rise
There is no doubt that attacks of all kinds are on the rise. The Department of Homeland Security has been responding to intrusions on oil pipelines and electric power organizations at “an alarming rate,” according to an agency report last December. Some 198 attacks on the nation’s critical infrastructure systems were reported to the agency last year, a 52 percent increase from the number of attacks in 2011.
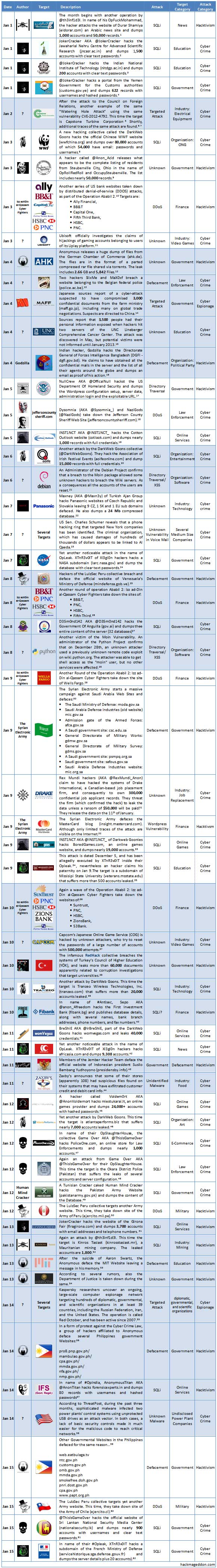
However, digital security isn’t a question of probability, it’s something you should be prepared for no mater how secure you think your website is. Let’s just take a look at a timeline of January 2013 to give you an example of the variety and types of major websites that were compromised:

Important Things To Keep In Mind
- This is just a sample list of major websites that were successfully hacked.
- This list is comprised of submissions by hackers. In other words, there were a lot of other hacking attempts/successes that were not reported.
- This is a very small fraction of websites hacked just within January 2013. One month.
- 50 million people’s data and personal information were compromised in just one attack alone.
Common Ways Individuals Compromise Their Security
In order to prevent mistakes, you need to know what they are. While there are a variety of things individuals can do to create multiple layers of protection against security breaches, here are some common mistakes that are made:
Accessing An Account via An Email Link
The most common Internet security mistake is accessing a personal account via an e-mail link. Targeted phishing scams have become increasingly sophisticated and rely on URL cloaking software to make malicious links look legitimate. Any time someone receives an e-mail directing them to access an online account, it is important to enter the URL manually. This will ensure the user knows exactly where they are going and will eliminate one of the most prominent Internet security risks.
Using A Single Password For Every Account
Another common Internet security mistake is using the same password for every account. While the number of online accounts the average person signs up for is larger each year, it is important to create a different password for each account. Using the same password over and over is a mistake because if one account becomes compromised, the hacker then gains access to every other account. An easy way to avoid this mistake is by using a password generator.
Assuming Internet Security Software Is Perfect
The most understandable digital security mistake is assuming Internet security software is perfect. Internet security companies spend a great deal of time and money advertising their services. At a glance, it seems like today’s Internet security software suites protect users from every conceivable threat. Unfortunately, much of this software is reactive rather than proactive. This means, the software cannot protect users until the threat has been identified. While using this type of software is incredibly important, it shouldn’t be considered a cure-all.
Clicking An Digital Security Related Pop-Up
To complicate matters, many cybercriminals leverage the threat of Internet security issues to promote malicious software. Any time someone receives an advertisement or pop-up related to Internet security, especially if it offers a free security scan, it is important to ignore it. If someone is interested in a free security scan, there are a variety of free trials from legitimate companies that can be accessed directly from the company website.
Assuming Online Shopping Is Always Safe
There is no doubt e-commerce websites go to great lengths to protect their customers’ personal information. With so much emphasis placed on protecting customers, many people assume that all online shopping is safe. The truth is, new fake e-commerce websites pop up every day. Data can be stolen when it is transferred between the user’s device and a legitimate e-commerce store.
Downloading Free Software
While free Internet security software can be particularly dangerous, downloading any type or free software poses an Internet security threat. It is important to only download free software from reputable sites and always do a few minutes of research to ensure the free software does not have a history of causing problems. All of these Internet security mistakes can easily be avoided by implementing safe browsing practices and taking the prospect of online protection seriously.
Not Keeping Software Up-To-Date
If you are running old versions of software chances are it’s insecure, make sure you upgrade to the latest release. Most updates to the software are security or functionality related, which means if you aren’t running the latest version you are likely to have missed a few security fixes.
Using The Wrong Browser
During a 2011 hacker conference, Pwn2Own, hackers attacked four popular browsers:
- Internet Explorer
- Apple Safari
- Mozilla Firefox
- Google Chrome
The hackers were able to quickly compromise Internet Explorer and Safari. In fact, these hackers were able to hack the browsers so thoroughly that they managed to write files on the hard drive of the computer they were attacking. Interestingly, Chrome and Firefox both resisted hacking attacks during the exercise. Regardless of the browser, manufacturers are always working to ensure users can enjoy surfing the web safely and securely—and that’s the good news. The bad news, as the Pwn2Own conference revealed, is that cybercriminals worldwide are also working hard to figure out new ways to hack your browser.
Third-Party Scripts And Code
Plugins, widgets or any other code (including free templates and themes) you install are written by other people under unknown circumstances. Some may be great, some may be full of holes. Be sure to research any code you want to use that you didn’t write yourself. Even a few Google searches should help you find out how secure the code you are using is.
Your Website Is On WordPress
I won’t get into too much detail for the purposes of this blog entry, but WordPress is notorious for being hacked due to gaps in the structure of its environment. In fact, there are over 5 million results in Google for “Prevent WordPress Attack.”
I deal with potential clients every day who have a website that exists on WordPress and love it. I’ll admit, WordPress is extremely user-friendly, easy-to-update, and with the right designer can look fantastic on the front end. However, here are some hard truths about WordPress.
WordPress has either no, or severely limited:
- Document management
- Workflow management
- Digital asset management
- Link management
- User management
- ESI Caching / CDN ability.
- WYSIWYG editing
- Single Sign-on
- Multi-side Admin
- Publishing options
- Access Management
- Application
- Multi-lingual
- n-to-n content sharing
- Reporting
Whenever a client comes to us requesting their website be built on WordPress, the first recommendation we make is that they opt for a true CMS. Although WordPress has been taking steps to upgrade their user authentication system, it’s by no means perfect; and while no system may ever truly be “perfect” WordPress is just a magnet for hackers. For example, in April 2013, a massive botnet of tens of thousands of machines hacked into weak password-protected “admin” accounts of the popular blogging platform – compromising thousands of users and their websites.
I run into programmers all of the time who are WordPress advocates, but from a security standpoint? It’s a BLOGGING PLATFORM, not a TRUE CONTENT MANAGEMENT SYSTEM.
Mediaura Makes Security Our #1 Priority
There are just some examples and tips. You do not have to spend thousands of dollars a month on your internet security, but you do have to make an investment. Cheap, budget website platforms and hosting solutions may seem attractive at first, but trust me, those savings won’t seem so spectacular after you’ve damaged your bottom line and the future of your business because your website and/or database have been compromised.
When your website is down, even for a mere moment, it compromises a lot more than your website. It negatively affects your brand identity, consumer confidence, it attracts MORE hackers (because trust me, they share information), etc. Don’t put your business at risk.
Mediaura takes your digital security very seriously because we don’t want to see your reputation and hard work get destroyed due to a targeted attack on your system.
We built our own virtual private cloud with enterprise-level hardware and cutting edge technology. Housed at Peak10, our solution includes multiple levels of redundancy and security that are typically only available to large enterprise clients, packaged as an affordable SMB offering.
The Technical Details
We utilize Dell Enterprise servers, switches, and SANs to create our own virtual cloud with VMWARE. The system has been built with redundancy, security, and speed as key priorities. There is no single point of failure, each system is isolated from others within our cloud for security, and our systems are not over-booked. Because of this, you get the uptime and speed you need, without the hassle of managing it yourself or hiring a full time IT person to manage it for you. This is a turn-key solution, which means there never be any finger-pointing when your online reputation is at stake!
The Mediaura Difference
Other hosting providers expect you to manage your own system on their hardware, including backups and digital security. If there is an equipment failure you are likely to be offline for hours or more. With our managed hosting solution, all failovers are resolved within 30 seconds and backups are handled automatically. We have 24/7 monitoring of our equipment, software, and network traffic.
Secure, hardware firewall access is enabled on all of our solutions. We support OpenVPN and IPSEC for remote access.
At Mediaura we understand that Digital Security can seem overwhelming. That’s why partnering with a digital agency that not only understands the industry but also places your security at the top is a smart decision.
Contact Us, so we can price out an affordable and reliable package for your website, mobile app, web application, or intranet file system today.

